The Impetus for Data Access Governance
In the early 2010s, the focus of data security and protection began to expand from records in database applications, termed as “structured data,” to file-based data known as “unstructured data.”
Following some high-profile data breaches, many organizations learned the hard way that their sensitive information wasn’t just the personal identifiable information (PII) of their employees and customers. It was also the organizations’ “crown jewels.” Setting the organization apart competitive, it contained marketing plans in presentation files, merger and acquisition plans in word processing files, yet-to-be-released sales numbers in spreadsheets, and other confidential information inside unstructured data.
Gartner soon designated a new market segment of software for identifying and securing sensitive unstructured data, christening it “data access governance.” According to Gartner: “Data access governance (DAG) provides assessments, management, and real-time monitoring for unstructured and semistructured data in file repositories. Its primary purpose is to determine, manage and monitor who has access to which data, rectify oversharing and secure usage of data with generative AI (GenAI). DAG provides an audit trail of access and permission activities.”1
OpenText and DAG
Long before the designation of the DAG market segment, engineers who now develop software for OpenText were building identity-based reporting and management software for unstructured data, which identified access risks, remediated improper access rights, moved data to more secure locations, and cleaned up expired data. These products are now known as OpenText File Reporter and OpenText File Dynamics and are offered together as OpenText Data Access Governance.
OpenText Data Access Governance identifies, secures, and protects an organization’s sensitive and high-value unstructured data from unauthorized access. This includes PII, as well as sensitive information within unstructured data. OpenText Data Access Governance uses an identity-based approach to specify where organizations store known confidential files. It can also help you determine who has access to them, make needed changes to locations and permissions, and ensure that sensitive and high-value data remains secure from unauthorized access.
Expanding DAG Capabilities through Product Integration
Yet, Data Access Governance and other OpenText Cybersecurity personnel recognized that OpenText, as a developer of additional data discovery and identity governance technologies, had everything to deliver a much broader DAG solution capable of:
- Running data discovery software to identify individual files containing sensitive information before running OpenText Data Access Governance component products.
- Performing access reviews for compliance certification and attestation after running OpenText Data Access Governance component products.
The challenge was in integrating all these OpenText technologies. That’s where the OpenText Data Access Governance engineers stepped in.
Integration Work
The OpenText Data Access Governance engineers began the first phase of integration work in 2018 by enabling the export of reports and converting Windows NTFS file system permissions classifications from File Reporter to OpenText Identity Governance. This enabled Identity Governance to conduct access reviews on unstructured data repositories.
The team followed up this effort with additional integration work in File Reporter in 2025 that provided the ability for OpenText Core Data Discovery & Risk Insights (CDDRI) to export workbooks from CDDRI into File Reporter, where the latter could specify who had access to the sensitive files that CDDRI located.
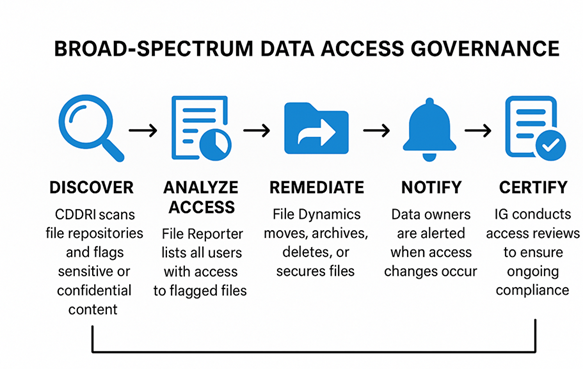
The capabilities OpenText data access governance solution exceeds the very definition of DAG, At OpenText we refer to it as “Broad-Spectrum Data Access Governance.”
How Broad-Spectrum Data Access Governance Works
Once CDDRI has performed data discovery, identified files with sensitive content, and put the results in a workbook, a new Report Permissions option appears via File Reporter. Clicking this option triggers File Reporter to report all users with access to these sensitive files. Users can generate these reports as simple reports or through rich graphical analytics via Power BI.
With the information from the report, File Dynamics takes any needed action through policies that you create. These policies can move files to more secure locations, archive or delete expired files, and secure folders and shares storing confidential information.
Finally, the OpenText broad-spectrum DAG solution lets you perform access reviews on unstructured data by making unstructured data folders and shares visible for review and converting and consolidating NTFS permissions to the Identity Governance permissions of Read, Write, and Change Permissions. This enables organizations to certify and provide attestation of compliance with regulations that only authorized users have access to confidential and sensitive files.
The DAG Message is Resonating with our Customers
Until now, we’ve limited our discussions of Broad-Spectrum DAG to a select number of OpenText customers. However, the response has been overwhelmingly positive. With organizations storing many terabytes or even petabytes of unstructured data, a lack of understanding of what that data contains, not knowing who has access to it, and the risk of a data breach or a fine, the message is timely and resonating well.
OpenText World 2025: Elevate together
Join us in Nashville November 17-20 for 3 days of AI innovation, bold ideas, visionary speakers, and great music, of course. C’mon, let’s go!
Register nowLearn more about Broad-Spectrum DAG at OpenText World
Broad-Spectrum DAG will be covered in multiple sessions at this year’s OpenText World, November 17-20 in Nashville. If you can’t make it there, we’ll be talking about it more in upcoming webinars. And your OpenText account representative can provide additional insight and line you up with a technical expert to get your questions answered.
1Gartner, Hype Cycle for Data Security Technologies, 2025, Andrew Bales, 10 July 2025 – ID G00828131



