Last November at OpenText World, we introduced attendees to new OpenText product integrations for identifying and securing sensitive unstructured data. In what we termed “Broad-Spectrum Data Access Governance,” the solution not only meets the requirements for data assessment, management, and monitoring in data access governance (DAG) as defined by Gartner1, but also expands those requirements to include data discovery and certification and attestation through access reviews.
The Broad-Spectrum DAG introduction included a blog post detailing the product integration work between OpenText Core Data Discovery & Risk Insights, OpenText Data Access Governance, with its comprising products – OpenText File Reporter and OpenText File Dynamics, and OpenText Identity Governance.
Since the announcement, people have been eager to see how Broad-Spectrum DAG works. We’ve demonstrated it to a few customers and even made a video. Still, we’re really excited about an interactive demo that you can run yourself.
The scenario in the demo is as follows:
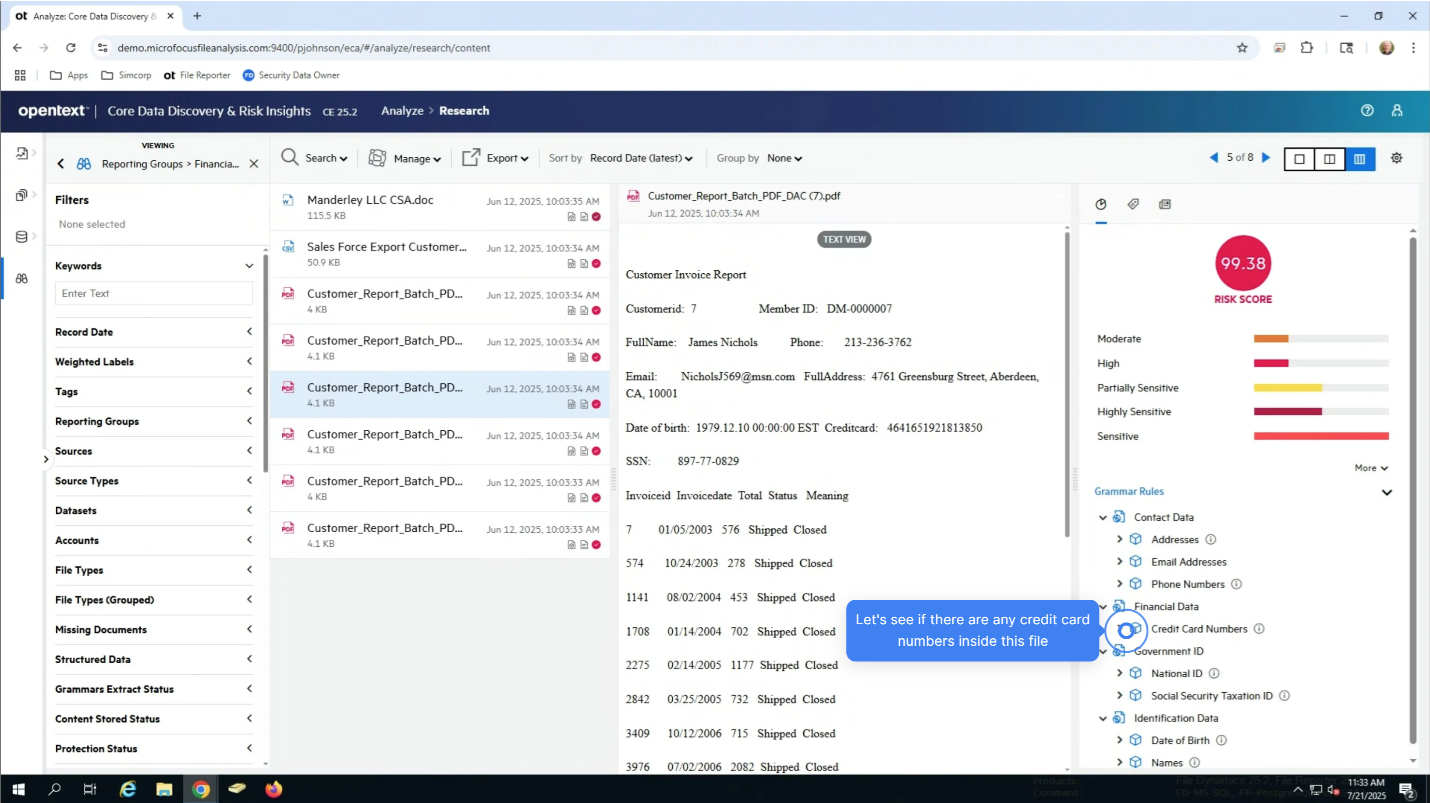
A security analyst needs to:
- Identify sensitive files located in the Finance folder. Also, to classify and tag these files based on their associated risk (using OpenText Core Data Discovery & Risk Insights).
- Identify who has access to these files and determine how these users are gaining that access (using an integration with File Reporter).
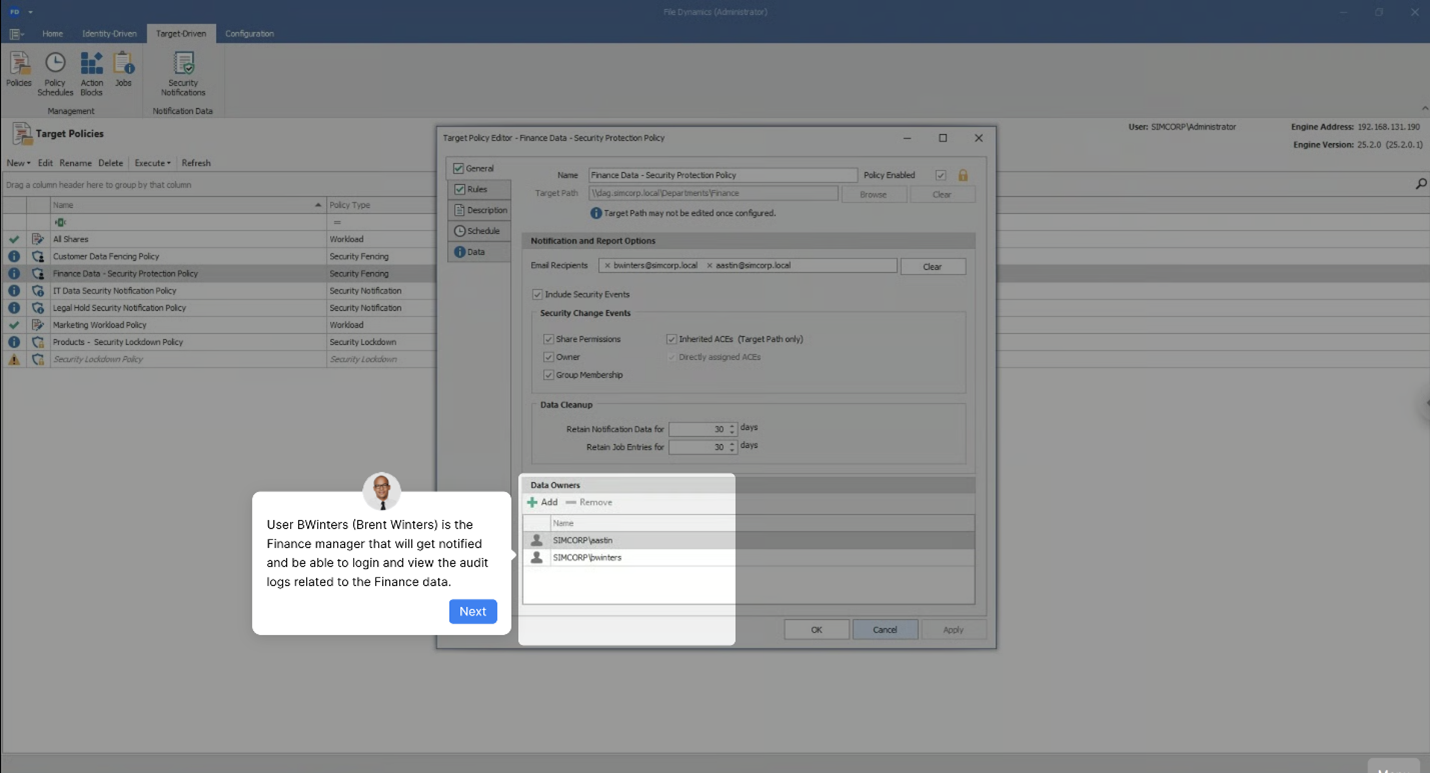
A security data owner then needs to:
- Monitor and protect the Finance folder data so that only authorized users have access to these sensitive files (using OpenText File Reporter and OpenText File Dynamics – components of OpenText Data Access Governance).
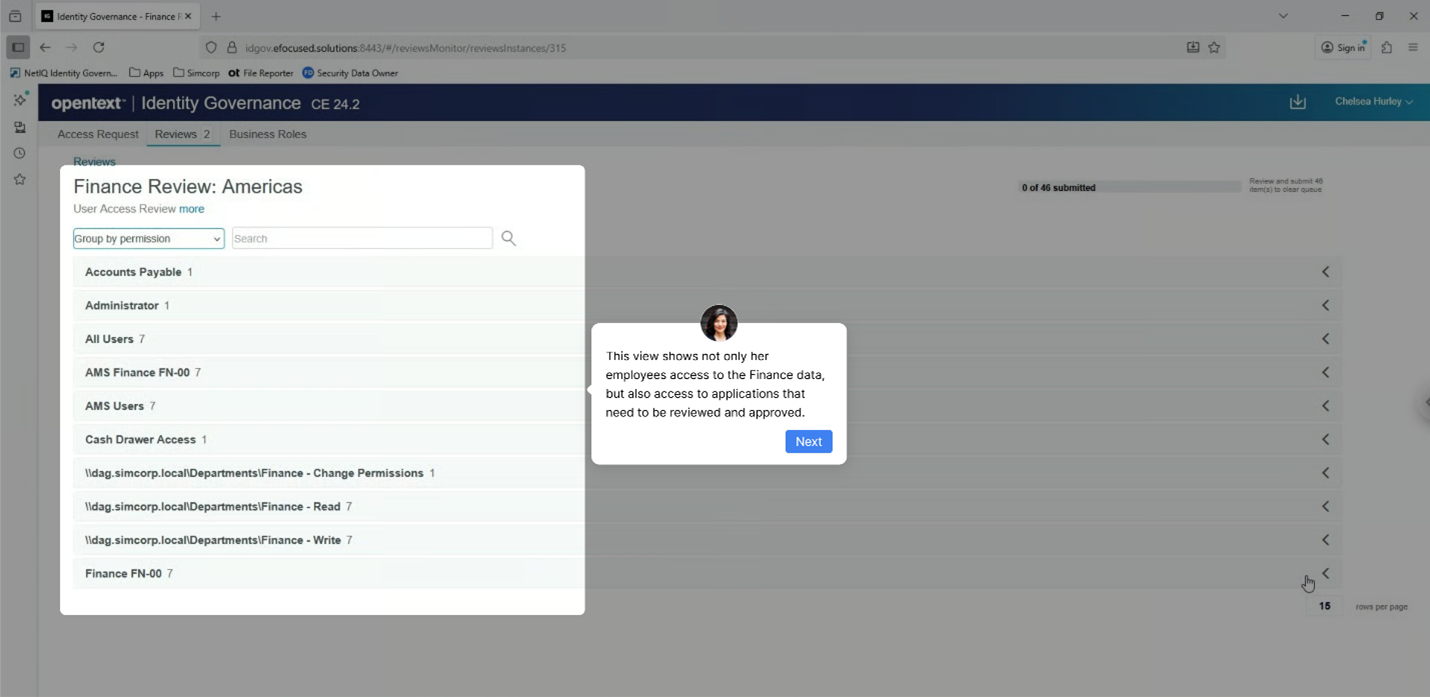
A line-of-business manager then needs to:
- Provide multiple line-of-business managers with the ability to perform access reviews and provide attestation that only authorized users have access to these sensitive files (using an integration between OpenText File Reporter and OpenText Identity Governance).
When you run this interactive demo, you play the role of each of these individuals through the interface of each product.

To run the interactive demo yourself, visit this link.
1See Gartner, Hype Cycle for Data Security Technologies, 2025, Andrew Bales, 10 July 2025 – ID G00828131



