
New era of concern
In 2023, the world saw a 72% increase in data breaches from 2021, which held the previous record. Meeting risk and security standards are table stakes for companies of all sizes. In fact, cybersecurity risks are more prominent than ever. A whopping 95% of cybersecurity issues are traced to human error, and 93% of cyber leaders believe global geopolitical instability is likely to lead to a catastrophic cyber event in the next two years.
In this new era, AI powered cyber-threats are on the rise. New challenges include criminal AI-based social engineering, realistic content generation, a rise in attack scalability, and enriched adaptive evasion. In fact, there is a whole practice of “Dark AI” prevalent on hack forums. Popular LLMs are programmed not to respond to illegal and controversial prompts to remove ethical safeguards, but criminals are jailbreaking, and malicious actors are clearly using AI tools.
It’s time to embrace the new era of concerns.
Market dynamics –> Go-forward security priorities
Security fragmentation –> Integrated security and governance
Increasing frequency of cyber attacks –> Security posture management
Ransomware and data breaches –> Faster incident response
Get AI ready –> Secure information management
Security skill shortage –> Secure by design
New era of protection
The security posture for the future is thinking about all the elements:
X–Ingestion everything from device endpoints to networks to applications to web and email, embrace the challenge to protect it all through robust identity access management and data security.
D–Detection quickly and repeatedly perform tasks to find vulnerabilities (e.g., map to schema, telemetry enrichment, parsing, analytics, cross-correction, and alert prioritization)
R–Response ensure there are defined ways to triaging issues, automating workflows, hunt and investigate, providing surgical responses and performing schedule scans.
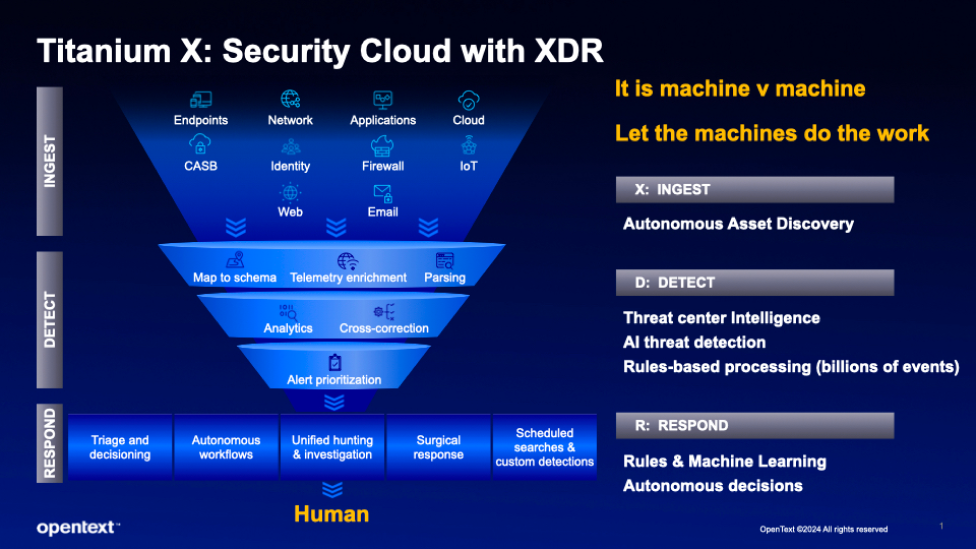
For enterprises of all sizes, billions of events are process daily. To be proactive versus reactive, we must let the machines do the work. Machines can help us take it to the next level:
• Autonomous asset discovery–finding points of vulnerability across an IT estate
• AI threat detection–anticipating malicious acts and protecting against them
• Rule-driven and machine-learning responses–at scale, using machine learning and predictive analytics to predict deep fakes
Getting AI-ready means to lead your organization through understanding, accepting, and proactively protecting against new types of security concerns. Learn more about how you can get started with OpenText™ Cybersecurity. Our portfolio of solutions is unique in how we anchor on information security as our DNA, how we focus on real time AI threat detection, how we offer a high-efficacy end-to-end portfolio, and how we have a seamless platform experience.
Information management is a pre-requisite of AI. Help your organizations ensure cybersecurity protection is omnipresent along with AI. The future of machine vs. machine will heighten the need for cybersecurity across all domains.
Get more information about AI threat detection from OpenText™ Cybersecurity Aviator and our Cybersecurity portfolio. View OpenText World Europe keynotes to learn more.



