Security
Three key aspects of being a threat hunter
In today’s digital landscape, the role of a threat hunter has become indispensable. As cyber threats grow increasingly sophisticated, the need for professionals who can…

Connect with OpenText at Google Cloud Next 2023
Google Cloud Next 2023 is back in-person on August 29-31, in San Francisco. This is Google’s largest annual event with more than 15,000 IT, line…
• 4 minute read

What’s new in Application Modernization & Connectivity
The latest OpenText™ Cloud Editions includes updates to AMC’s COBOL, Enterprise Suite and Host Connectivity offerings – designed to support IT leaders in their continuous…
• 3 minute read
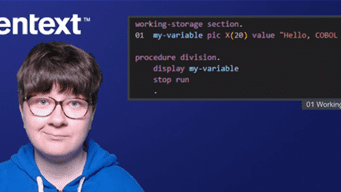
OpenText innovations nurture talent to accelerate application modernization
Welcome to Visual COBOL 9.0 and Enterprise Suite 9.0, the latest releases delivered as part of our OpenText Cloud Editions (CE) 23.3 innovations, designed to…
• 3 minute read

Obtaining a bearer token to enable API interaction
OpenText™ Network Detection & Response (NDR), previously known as Bricata Network Detection & Response, provides real-time network visibility, metadata generation and threat detection. Additionally, it…
• 6 minute read

To upgrade, or not to upgrade…that is the question for enterprise software users
Upgrading a major software application can be challenging. Many factors come into play, including budget issues, downtime, upskilling the staff, and addressing software and automation…
• 5 minute read

Government must view ESG in 3D
Citizens today are becoming increasingly aware of how their actions and the actions of the organizations they work with affect the world around them—a trend…
• 5 minute read

One, two, three…steps to improve your eDiscovery review database security
There are many good reasons to be proactive when it comes to securing our data everywhere it lives. In legal matters, we go from legal…
• 5 minute read

Recover your systems and data from disaster with confidence
Having a disaster recovery plan is critical to your organizations’ success. When a critical system goes down, whether from ransomware or natural disaster – you’ll…
• 4 minute read

Dissecting IcedID behavior on an infected endpoint
IcedID, also known as BokDot, is a banking trojan that was first discovered in 2017. It targets a victim’s financial information and it is also…
• 4 minute read

10 steps to combat the high cost of cyber insurance
As the frequency and scope of cyberattacks increases, so does the cost of cyber insurance. And the rise is dramatic. As discussed in The Wall…
• 5 minute read

The EnCase Evidence Viewer
OpenText™ EnCase™ Forensic software is one of the longest established digital forensic platforms on the market. It has been the primary tool of choice for…
• 3 minute read
Security Operations: Best Recent Reads
To help shed light on SecOps and the issues surrounding it, this blog post offers a roundup of some of the most insightful content published in various corners of our site.
• 4 minute read
Stay in the loop!
Get our most popular content delivered monthly to your inbox.
