Cyber-attacks are on the rise. Data breaches are becoming more common and devastating. Akamai’s State of the Internet Report revealed that hacker attacks on websites rose by 75% in the final quarter of 2013. As digital technologies evolve, information security breaches are becoming more sophisticated, multi-stage, and highly targeted.
From organized crime syndicates to hacktivists, vulnerabilities permeate all levels of IT systems—at great cost. Estimated financial impact of cybercrime to the global economy ranges from $375 billion to $575 billion annually. And this figure doesn’t even reflect estimated losses of trade secrets, intellectual property, and other non-financial impacts, which peaks at $2.2 trillion annually (PwC). To mitigate this corporate threat, world-wide investment in information security is expected to reach $76.9 billion by 2015.
Enterprises and government agencies are under virtually constant attack. As gatekeepers of highly sensitive data and confidential assets, cyber security is a top priority for government agencies. In a recent study, half of cyber security professionals in the U.S. Federal Government agree that their agency is likely to be the victim of a denial-of-service attack in the next 12 months. What is especially concerning is that, while they foresee future breaches, the majority of participants in this study feel unprepared: 74% say they are not prepared for an international cyber-attack; 74% are not prepared to support secure access for mobile devices; 70% are unprepared for a denial-of-service attack; and 70% are not prepared to secure cloud computing environments. These are disconcerting numbers.
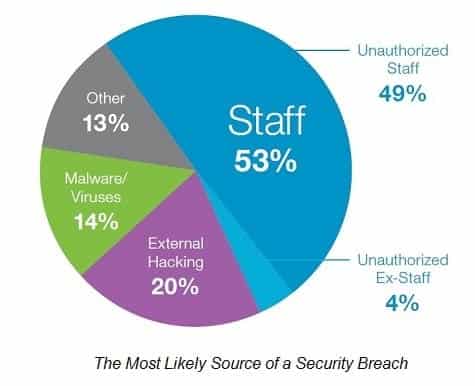
The same study revealed one of the major catalysts of security breaches—the end user (in other words, your employees). While many security risks come from outside an organization, many breaches occur from within. The rise of the mobile workforce contributes to this, increasing risk through the lack of clearly defined or implemented Bring-Your-Own-Device (BYOD) policies, lost or stolen devices, and the accidental sharing of confidential information across devices.
To their disadvantage, agencies fail to take the end-user experience into account when deploying cyber security solutions. As a result, users often circumvent security measures, making their agencies vulnerable to data theft, data loss, and denial-of-service attacks. While federal agencies are looking for mechanisms to fight information security threats, they are shifting to a distributed approach that combines top-down governance and bottom-up security mechanisms, fully integrated in an Enterprise Information Management (EIM) system.
Taking the end user into account, EIM is designed to protect information where it is used: at the point of interaction (with the end user) in the application itself. Mechanisms like access and permission rights, information audit, and secure information exchange are built right into the system to secure content. Technologies such as records management and auto-classification provide a non-intrusive solution that eliminates the need for business users to sort and classify content, while enabling agencies to establish highly defensible, completely transparent records management as part of a broader information governance strategy. Automating the ability to identify records and apply classifications eliminates the burden on the end-user, increases productivity, and helps to ensure content is securely managed and disposed of, throughout its lifecycle, in any format.
Government agencies are challenged to protect personal data and comply with privacy and other regulations, while permitting open access to government information. From the top-down, EIM offers a risk-based approach to information security and ensures the capabilities, programs, and processes are in place to assist governments in maintaining the confidentiality, integrity, and availability of their information. EIM helps agencies find a fine balance by empowering both the organization and end users with the confidence that their information is secure.
With security threats looming on the horizon, the value of information cannot be considered outside of the context of security. EIM is a key component in a comprehensive information security arsenal—alongside established policies and procedures, employee training and awareness, and continual monitoring of security risk and the program as a whole.
You can read more about information security in the public sector in my book: e-Government or Out of Government and view our targeted government solutions.



