We are thrilled to announce the next generation of Audit Assistant, our innovative machine-learning–assisted auditing of SAST results. Fortify™ now unlocks and reproduces contextual awareness and security expertise from Fortify SAST results for the first time in the history of application security testing.
Why we did it
A fundamental problem with static code analysis has always been that it requires human auditing before the results are actionable. The action of auditing is a leading segment of non-value–added time.
What’s the value?
- Reduces the number of issues that need deep manual examination
- Identify relevant issues earlier in the SDLC
- Scale application security with existing resources
- Maintain consistency in auditing and reporting
- Increased ROI on existing Fortify products
Why Static Application Security Testing?
Static Application Security Testing (SAST) is the market of products and services that analyze an application’s source code, bytecode, or binary code for security vulnerabilities. The National Institute of Standards and Technology (NIST) notes that static analysis tools are one of the last lines of defense to eliminate software security vulnerabilities during development or after deployment.
These software security tools and services report weaknesses in source code that can lead to vulnerabilities an adversary could exploit, to the detriment of the enterprise. If source code implements weak security, the business is exposed to additional risk that is unknown without SAST. Static application security testing enables enterprises to know their risk, transform their security posture, and make informed decisions to protect the business.
Confirmation of software vulnerabilities
SAST reports categorize issues by their criticality. Issues must then be manually confirmed as exploitable, or marked as not an issue by expert application security auditors. There are many reasons underlying a determination of not an issue. While some findings are false positives, more often the finding is not relevant because of organizational policy or is not exploitable due to mitigations being in place, or the potentially vulnerable code being unreachable.
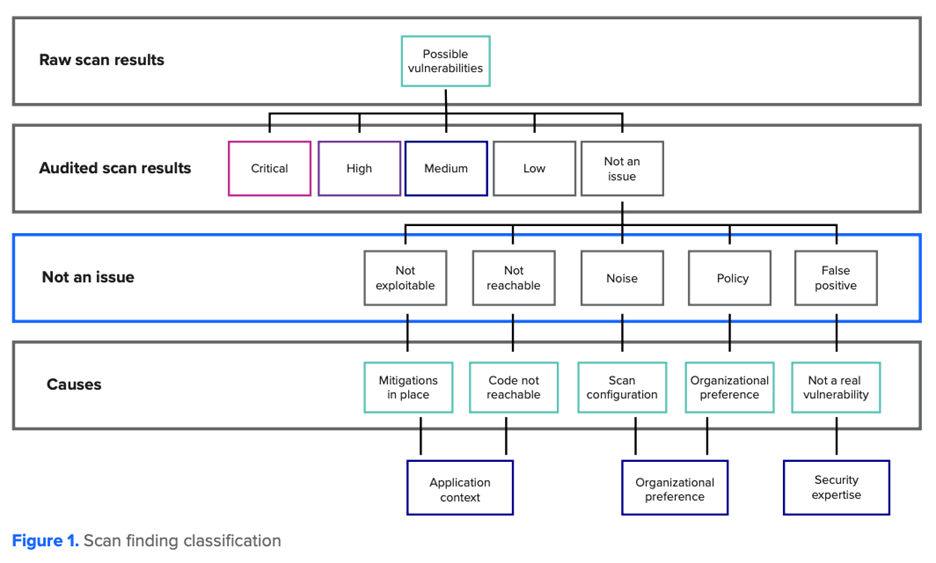
SAST tools report findings of potential vulnerabilities in an application by using different analysis methods such as taint, structure, or control flow analysis. Expert auditors are required to validate findings using details specific to their enterprise, such as the context of the application and deployment. When auditors determine a potential software security vulnerability is not an issue, the time spent on verification is non-value added time.
These time-consuming audits have traditionally come at significant cost to the enterprise and expose a fundamental challenge with delivering secure applications; tools and technology do not immediately produce actionable intelligence. The well-recognized cybersecurity skills gap adds to the challenge of software security assurance. Skilled security professionals rightfully command high salaries, and by definition even the best individual contributors cannot be effectively scaled to the enterprise’s needs.
Static analysis tools make the impossible job of securing code possible, and a skilled auditor’s software security expertise verifies actionable findings. Even the best security teams are ultimately limited by the human experience available, which often pales in comparison to the universe of potential software flaws to which the organization is exposed.
The next evolution of secure applications comes by leveraging machine learning to make the process of securing developing applications quick and efficient. These techniques extend the reach and better scale the expertise of the security professionals through the security development lifecycle.
Machine-learning and predictive analytics: the next generation of SAST
The actionable intelligence problem is addressed through the Fortify scan analytics platform. Fortify has been deploying and validating this approach with Fortify on Demand by OpenText™ for over over 5 years, and has been delivering monumental improvement to the issue auditing process.
This capability is now available to on-premises customers of Fortify Software Security Center via its Fortify Audit Assistant feature. Fortify Audit Assistant identifies relevant exploitable vulnerabilities specific to your organization, in new static scan results. It does this by employing scan analytics machine-learning classifiers that are trained using anonymous metadata from scan results, previously audited by software security experts.
Fortify Audit Assistant transmits only anonymized metadata derived from the scan results called anonymous issue metrics. Neither scan results nor code ever leaves the SSC environment. Issues indicated by the proven Fortify Static Code Analyzer are parsed by Fortify Audit Assistant into non-sensitive attributes.
These attributes include vulnerability category, severity, and measures of code and software security vulnerability complexity— such as the number of inputs, branches, method output types, programming language, file extension, and the analyzer that found the issue. In the case of training data, the auditor’s previous determination is also included. The anonymized issue metrics are sent to Fortify scan analytics to train and apply machine-learning classifiers, which identify issues with up to 98 percent accuracy.
After processing a new static scan result, audit assistant will add its prediction and prediction confidence to the scan results. Based on an organization’s risk tolerance and preconfigured confidence thresholds, those issues will then be categorized as Exploitable, Indeterminate, or Not an Issue.
- The prediction value indicates whether Fortify Audit Assistant considers the issue Exploitable, Not an Issue, or if the prediction confidence falls below the threshold, Indeterminate.
- The prediction confidence represents the confidence audit assistant has in the accuracy of its prediction.
Without exposing sensitive or identifying information, Fortify Audit Assistant determinations are added back to the scan results and made available for review by an organization’s security auditors. Anonymized metadata remains protected in the TLS encrypted communication channel throughout its transmission through the cloud. Transmitting only the anonymous issue metrics allows the enterprise to scale its software security assurance program and decrease its risk while not allowing sensitive data outside of its normal protections. By deriving issue metrics from the customer scan results, audit assistant empowers the enterprise to leverage the knowledge of thousands of security professionals who have collectively evaluated billions of lines of code.
Without expanding headcount or allocating additional budget, the enterprise’s application security program becomes more efficient and effective through machine learning. This paradigm shift in SAST from scarce human expertise to the limitless scalability of artificial intelligence reduces non-issue findings by up to 90 percent.
Conclusion
This paradigm shift in static analysis dramatically increases return on investment as the time and cost to audit results decrease substantially. Enterprises now have the capability to leverage the knowledge of thousands of security professionals who have collectively evaluated billions of lines of code within their own software assurance programs through Fortify Audit Assistant.
Rather than reduce the breadth of security issues through limiting what analyzers report, Fortify has created the scan analytics platform to distinguish nonissues from real issues automatically. This innovative approach utilizes Big Data analytics to scale secure software assurance to the enterprise without sacrificing scan depth or integrity.
As organizations continue to transition to a DevSecOps environment, application security must be built into their processes. Fortify Audit Assistant directly helps automate the auditing process so deliverable and deployment schedules are met. Fortify Audit Assistant uniquely reduces the repetitive, time-consuming work of issue review through the scan analytics platform.
Enterprises no longer need to accept noisy scan results, make tradeoffs between scan comprehensiveness and time-to-audit, or negatively impact product delivery dates with scan review time. Classifiers trained on anonymous issue metrics reduce the expense of software security assurance programs without the risk of identifiable data transmitted to the cloud.
Organizations immediately reduce their overall security workload through vulnerability prediction by opting in to use the Fortify product line’s community intelligence classifiers.
Fortify was founded in 2003 and has been providing the industry-leading Fortify Static Code Analyzer tool for a scientifically sound approach to secure software development that enables meaningful and practical testing for consistency of specifications and implementations for more than a decade.
Learn More about Fortify’s Audit Assistant AI with this white paper.




